Data Finder Start 855-439-2490 Unlocking Contact Trace Insights
Data Finder Start 855-439-2490 integrates diverse data streams to reveal transmission paths and exposure windows. It translates case records, mobility signals, and temporal networks into real-time analytics that yield prioritized alerts for responders. The approach emphasizes modularity, privacy-preserving governance, and auditable traceability to support scalable deployment. Its effective use hinges on clear metrics and governance, yet practical deployment raises questions about resource allocation and verification that merit further scrutiny.
What Data Finder Unlocks in Contact Tracing
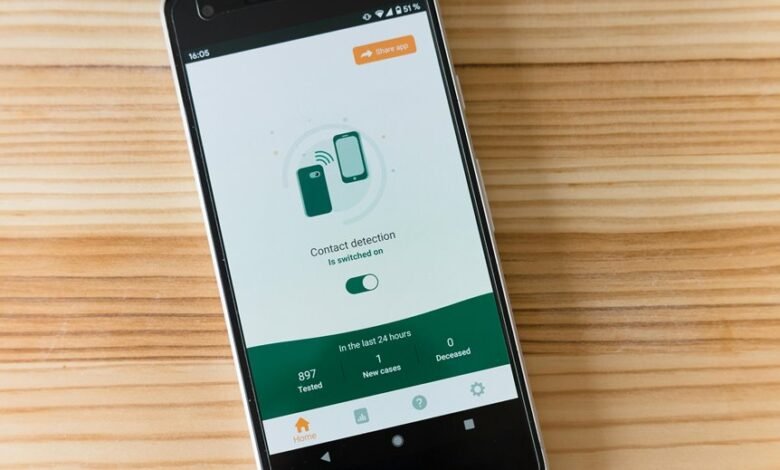
A data finder elucidates the specific data types and sources leveraged to map transmission paths, identify high-risk contacts, and quantify exposure windows. The approach integrates case records, mobility signals, and temporal networks to reveal actionable patterns. Data unlocks, trace insights, and accelerates assessment. In this framework, data finder capabilities underpin transparent, precise, and scalable contact tracing without compromising privacy.
How the Analytics Translate to Faster Responses
Analysts translate complex data streams into actionable tempo by prioritizing speed without sacrificing accuracy: real-time analytics distill case trajectories, exposure windows, and contact networks into prioritized alerts, enabling responders to triage high-risk contacts, initiate rapid notifications, and allocate resources where they will have the greatest impact.
The approach emphasizes data precision and speed optimization to shorten response cycles while preserving reliability.
Mapping Networks Without the Jargon
The analysis focuses on network topology and data dictionaries to define connections, roles, and attributes succinctly.
This approach enables independent evaluation of spread dynamics, trace efficiency, and anomaly detection.
Privacy, Scale, and Practical Deployment Strategies
Privacy, scale, and practical deployment strategies demand a balanced assessment of data governance, system performance, and operational feasibility. The analysis emphasizes privacy preserving approaches that minimize exposure while maximizing actionable insight. Architectural choices should prioritize modularity and auditability, enabling iterative deployment. Operational scalability hinges on provenance, traceability, and resource-aware optimization, ensuring compliant, robust, and scalable traceability without compromising freedom or analytical rigor.
Conclusion
Data Finder integrates diverse streams—case records, mobility signals, and temporal networks—to map transmission paths and quantify exposure windows. Analytics translate into prioritized alerts, enabling faster, targeted responses. The approach emphasizes modular architecture, privacy-preserving governance, and auditable traceability, supporting scalable deployment and efficient resource use. By distilling complex trajectories into actionable insights, responders gain clarity amid uncertainty. Is a data-driven, transparent workflow the fastest route to curbing outbreaks and safeguarding communities? This concise, evidence-based conclusion answers with measured confidence.






